Видео с ютуба Cryptography Audit

What is Cryptography | Cryptography Explained | Cryptography Basics | Intellipaat

Why Quantum-resistant cryptography is an urgent need | Encryption Consulting

Smart Contract Audits, Security, and DeFi FULL Course | Learn smart contract auditing
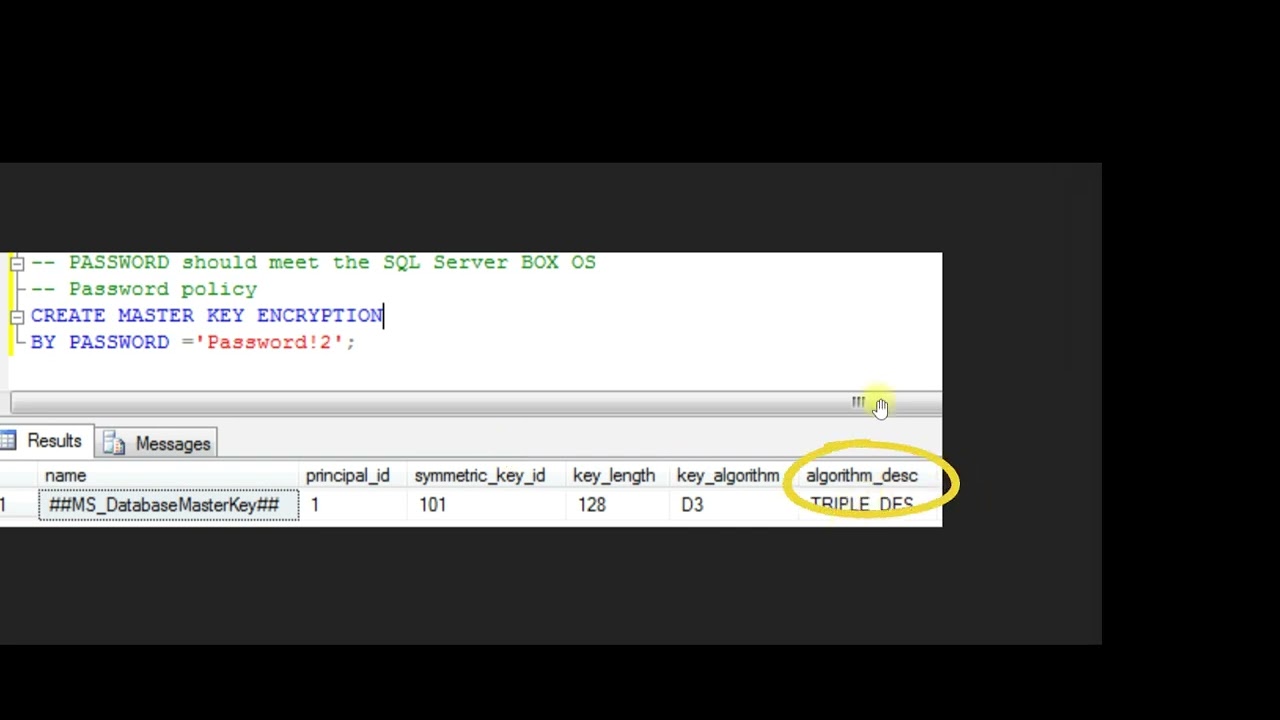
Lecture 13 - Step 3.8 - Auditing Encryption Algorithm

Auditing Mixes - Applied Cryptography

Encryption Ssecurity Audit Checklist

Auditing Cryptography: #Zcon2Lite

Cryptography Fundamentals 2022

GopherCon 2025: The Go Cryptography State of the Union - Filippo Valsorda
Why Audit Encryption In Cyber Warfare?

Understanding Cryptography for Offensive Security w/ Ayub Yusuf

Основы криптографии Ethereum

Integrating Cryptography Audit Standards into CI/CD

Auditing Tradeoffs - Applied Cryptography

WEBINAR RECORDING: What is FIPS Cryptography? How to get FIPS 140 Compliance?

Cryptographic Control and Encryption Policy Walkthrough

Meetup 009: High Assurance Cryptography and the Ethics of Disclosure w/ Nadim Kobeissi
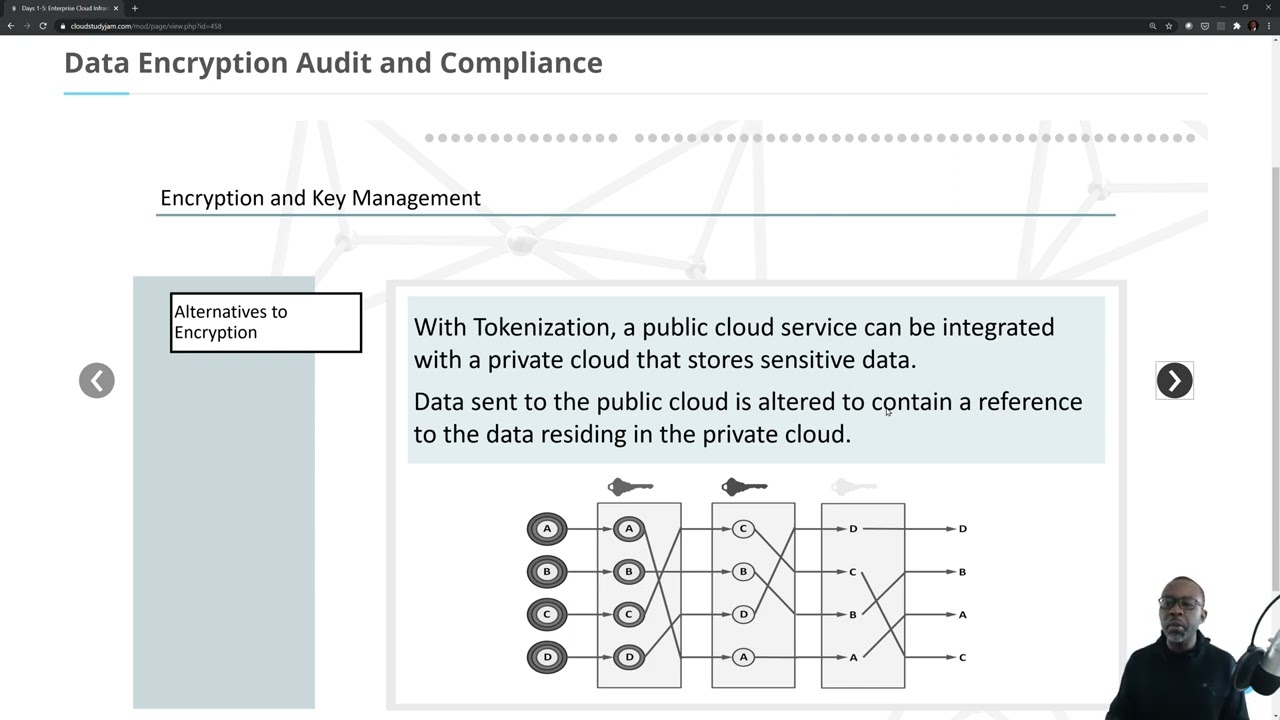
Data Encryption, Audit and Compliance

What is database authentication, authorization, encryption, audit logging? (ft. CockroachDB)

Cryptography Inventory - files or applications?